When guarding against malware attacks, we often worry about weaknesses in our IT infrastructure — but a growing number of attacks aren’t targeting our networks, they’re targeting us as people.
Criminal actors use social engineering techniques to trick people into sharing their login credentials for their email accounts, financial services and SaaS solutions. They are then using these credentials to gather information, gain access to more accounts and demand ransom.
We’re here to help with fresh insights on cybersecurity and useful tips on how to avoid social engineering attacks.
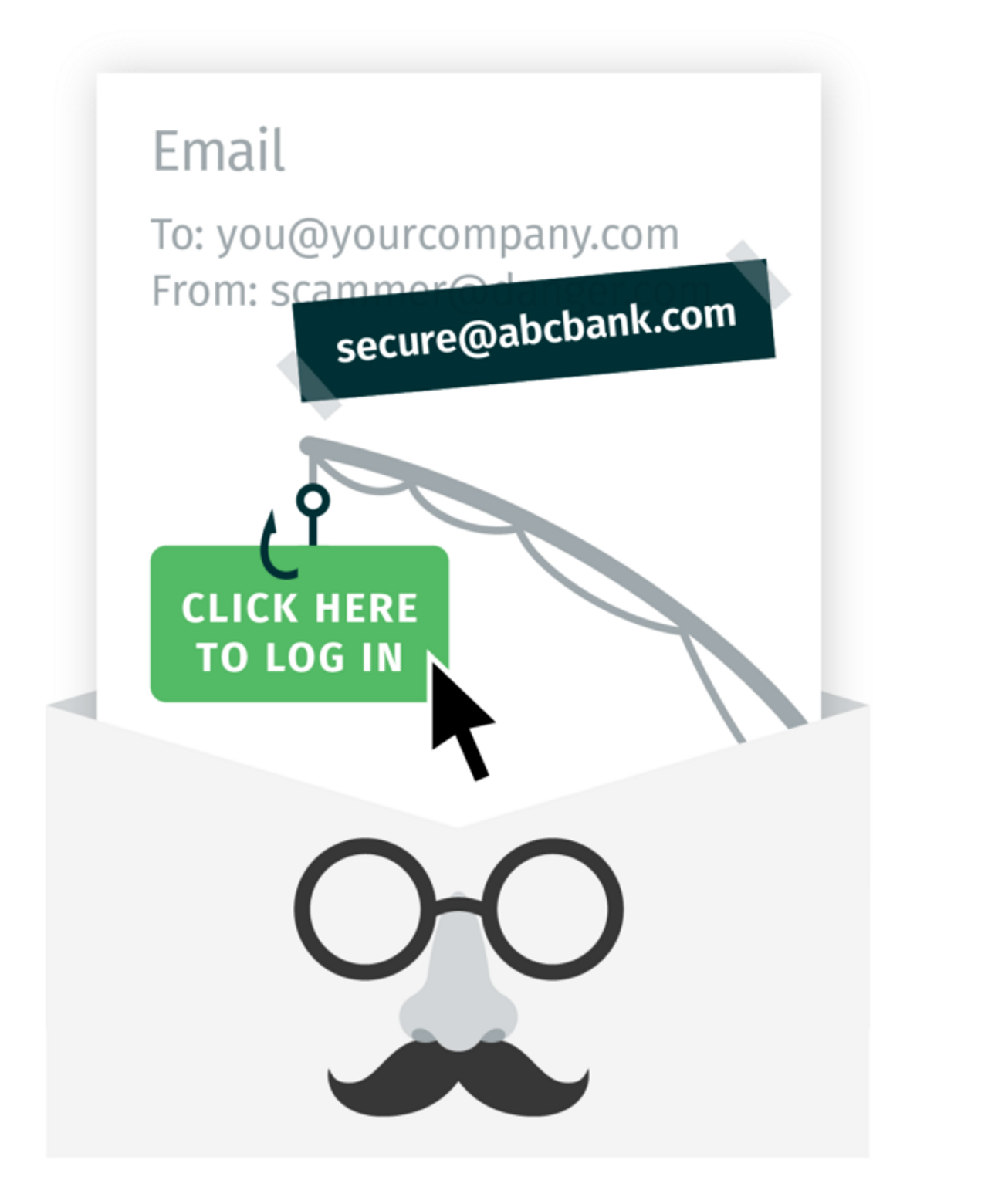
How spoofing works
Cybercriminals use forgery techniques to manipulate the headers of emails in such a way that they seem to be from someone else. For example, a cybercriminal may discover that you are a customer of ABC Bank. They may then send you an email from their own address, but manipulate the address or the code of the email so that when you receive it, your email client displays the email as being “FROM” ABC Bank.
The body of the fraudulent email may request that you CLICK HERE and input your login credentials in order to receive a payment. When you click, the email will send you to a dummy site made to look like an ABC Bank webpage. When you input your credentials, the cybercriminals will now have your account name and password, which they may use for a variety of criminal ends.
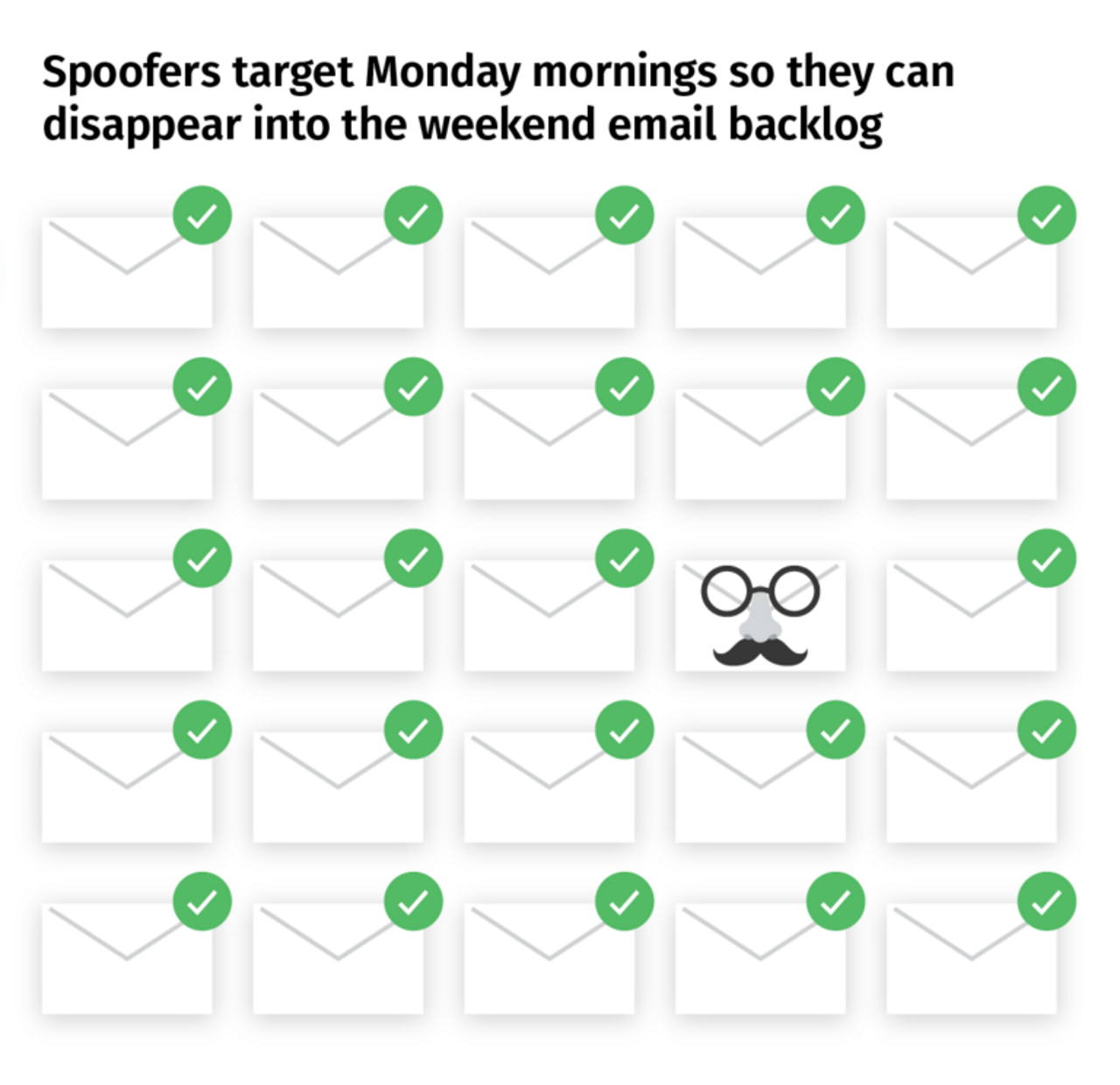
Spoofers follow a pattern of behavior designed to maximize their effectiveness. According to the Proofpoint “Human Factor” report, 95% of spoofing emails are sent during the work week, with the majority of those sent on Monday morning. Spoofers target the work week because recipients will be busy and stressed, and less likely to carefully read each email. They target Monday mornings to take advantage of recipients' attempts to quickly click through and clear their email backlogs.
According to the report, people working in finance positions are the most highly targeted group for social engineering attacks.
Can your SaaS providers stop spoofers?
Unfortunately, no company is immune from being spoofed. In a spoofing attack, it is actually the recipient's email client that is being tricked, the impersonated company has no direct involvement.
Although these types of scams are difficult to control, there are steps you can take. These security techniques may be helpful in discerning legitimate emails versus spoofs.
- Check with your IT department TO SEE if your company is using email security solutions and if they are working correctly.
- Confirm the sender’s identity before replying to email requests, opening attachments or clicking on links, even if they appear to come from a legitimate source.
- Consult your IT department about any phishing attempts.
Thank you for taking the time to read this article and arming yourself with the knowledge necessarily to defend yourself against fraudulent activity.

